Phishing is becoming more and more sophisticated and many potential victims tend to think that they know enough not to take the bait! However, a recent survey of over 1000 individuals showed that only 5% were able to spot ALL potential threats.
Since the number of spam emails sent daily is expected to increase to almost 190 billion a day through 2023 [1], it’s increasingly important to be able to spot the tell-tale signs of a fraudulent email and protect your personal and business data, and your technology from malicious viruses and malware.
We’ve put together a few tips that can help you identify a phishing attempt.
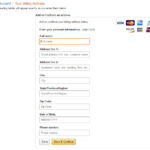
1. Confirming Personal Information – Often you will receive emails disguised to look authentic. They might mimic the style of your current company or an outside business such as a bank or credit card company. These emails may have requests for personal information that you would not usually provide, such as banking information or login credentials. It is important you don’t click on or respond to these emails. Before responding, determine the legitimacy of the email by contacting an organization directly or searching on the internet
2. Fraudulent Email and Web Addresses – Phishing emails often come from an address that appears to be legitimate, but at a closer glance can have some discrepancies. These emails may contain the names of genuine companies and might be made to replicate the company’s personal sites or email accounts. Brand logos and trademarks do not guarantee that an email is real. Hackers can use these images or download them from the internet to mimic an existing company. Even antivirus badges can be inserted into emails to persuade victims into thinking an email is from a legitimate source.
3. Grammar – Phishing emails can sometimes contain poor language in the body of the message. Grammatical errors and conflictive sentence structure are common in these fraudulent emails. A legitimate company would have constructed an outbound communication professionally and checked for spelling errors and other mistakes. While poor grammar is a giveaway, not 100% of phishing emails will have sloppy grammar, so it is important to keep on your toes.
4. Scenarios – Many phishing emails tempt to instill a sense of worry into the recipient. The emails may give a scenario that depends on you entering your credentials to solve it. For example, an email may state that your account will be closed if you don’t enter your personal information and act now. If ever unsure of what an email is asking of you and why, be sure to contact the company through other methods.
5. Attachments – If you receive an email from a seemingly random company you do not affiliate with, and the email references something unexpected, the attachment might include some malicious malware or virus. These attachments may contain a URL or trojan horse designed to compromise your system, if opened. Send these emails to your security team instead of attempting to open them yourself.
Because employees are the core of any business, they will be the main target for cyber-criminals. Making sure your people stay up-to-date with cyber-security knowledge, and teaching them to recognize threats is imperative to the security of your business. The threat landscape is constantly evolving and so should your approach to defense.
We offer security awareness training and phishing simulations to test employees on how they would respond to a real-life phishing attack. For the best measurement of all employees awareness, we send mock attacks at staggered times, to avoid the “prairie dog effect” where employees warn one another of the email.
Through these test campaigns we track and measure your employees strengths and weaknesses and once a learning gap is detected, we deliver interactive educational videos to the most susceptible users.
One of our most important roles as a technology service provider is to protect the assets of our clients. No matter how big or small your business is, a single compromised credential could put your entire business at risk. Give us a call to further discuss how we can help in protecting your business against cybersecurity threats and how we can make technology work for your business. Call us now at 732.780.8615
[1] https://www.statista.com/statistics/456500/daily-number-of-e-mails-worldwide/